Intel said today it is investigating an issue with Broadwell and Haswell CPUs after customers reported higher system reboot rates when they installed firmware updates for fixing the Spectre flaw.
The hardware vendor said these systems are both home computers and data center servers.
"We are working quickly with these customers to understand, diagnose and address this reboot issue, "said Navin Shenoy, executive vice president and general manager of the Data Center Group at Intel Corporation.
"If this requires a revised firmware update from Intel, we will distribute that update through the normal channels. We are also working directly with data center customers to discuss the issue," Shenoy added.
The Intel exec said users shouldn't feel discouraged by these snags and continue to install updates from OS makers and OEMs.
While Shenoy has not clarified what systems are experiencing higher reboot rates, it could only be Linux systems for which Intel started rolling out CPU microcode updates yesterday. These firmware updates mitigate the Spectre flaw.
AMD faces similar issues with Meltdown & Spectre patches
Earlier today, AMD also announced it will start shipping microcode updates that mitigate the same Spectre flaw.
AMD customers have too faced problems earlier this week when Windows updates meant to mitigate the Meltdown and Spectre flaws caused BSOD errors.
Microsoft paused the rollout of these updates to investigate. AMD said only AMD Opteron, Athlon and AMD Turion X2 Ultra families were affected.
Intel details performance hit for Meltdown fix
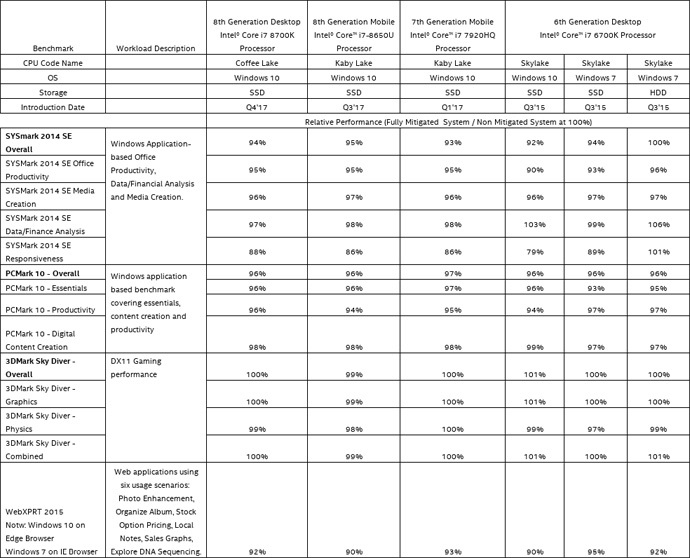
In a separate statement, Intel posted the results of a few benchmark tests it carried out for PCs patched against the Meltdown fix.
Intel said the older the user's processor is, the bigger the performance hit. Recent processors like the Kaby Lake series recorded a performance dip of around 5%, but the performance decrease goes into double-figures for older series.
Intel notes that performance for "web applications that involve complex JavaScript operations may see a somewhat higher impact (up to 10 percent based on our initial measurements)" while "graphics-intensive [workloads] like gaming or compute-intensive like financial analysis see minimal impact."
The results of Intel's benchmark are available in PDF format here.


Comments
Steve Holle - 6 years ago
It would be interesting to see what kind of hit AMD takes on the same benchmarks.
Warthog-Fan - 6 years ago
Looks like it might be a good idea to wait to install these updates until Intel works out the bugs?
SuperSapien64 - 6 years ago
I wonder how someone would even update this on Linux or the BIOS from an ASUS motherboard?
Warthog-Fan - 6 years ago
Good question about the ASUS motherboard, which is what I have in my desktop. I checked the ASUS web site and they have a BIOS update available which is associated with this problem but I'm a little leery about installing it in case it messes up something else. Neither one of their drivers for the sound system worked when I installed the motherboard and I had to revert back to the Windows 7 drivers. Doesn't give me a warm feeling.
TsofT - 6 years ago
"I wonder how someone would even update this on Linux or the BIOS from an ASUS motherboard?"
Linux fixes Meltdown by using a patched kernel (most, if not all, distros will install this by default or as part of their upgrade system). To fix Spectre Linux (like most OS) has the ability to load newer CPU microcode at boot time. Some distros like Ubuntu require installing the "iucode-tool" and "intel-microcode" packages which are not installed by default (note you will need to manually regenerate the initramfs after installing). You could instead upgrade the BIOS/firmware of your motherboard to get the newer microcode if an update is available, then you don't need the OS to load newer microcode at boot.
To check if you're protected against Meltdown then "dmesg | grep isolation" should give a message like:
Kernel/User page tables isolation: enabled
To check for Spectre fixes then do something like "dmesg | grep microcode" and check the version. If it's loading microcode at boot time you will see a message like:
microcode: microcode updated early to revision XXXX, date = whatever
SuperSapien64 - 6 years ago
Well I use a Ubuntu based distro LM and that sounds a little advanced for me. And as Warthog-Fan mentioned the BIOS option may not be the best option at this time.
cat1092 - 6 years ago
"Looks like it might be a good idea to wait to install these updates until Intel works out the bugs?"
Yeah, looks like their work is cut out. Intel should immediately cease further production & shipment of CPU's until this is fully contained, plus recall every unsold chip on retail shelves. No need for shipping more CPU's that has the bug inbuilt, kind of like giving a obviously intoxicated driver keys to their vehicle, knowing full well that danger is imminent.....and it is. Every one of these CPU's sold is another disaster waiting to happen. I've yet to read an article that's stated any new Intel releases are fully fixed at the hardware level, to include the i9 that's about to fall into the hands of many enthusiasts. Not a single one.
Intel's not going to stop.........unless an agency such as Homeland Security (or other agency as designated by Congress or POTUS) gets involved & they should......now, w/out delay & unannounced to Intel prior. This is not only a US wide, rather a Worldwide issue and since Intel obviously cannot govern themselves, needs a watchdog to ensure that no CPU with these flaws gets into any further customer's hands. Plus ensure that there's permanent fixes for CPU's in the market that's affected. Many are still running early Windows XP era computers, even if that OS is no longer installed. I'd say a good starting point would be P4 & newer, as many Linux users are still running these machines, as well as Windows 7 & newer on many Socket 775 builds, this post being penned via Windows 10 (1709) on a Q9650 system.
http://speccy.piriform.com/results/KrLOS6PonUgBCkyZLkrPJgv
Many of these systems are tough as nails and are going nowhere for at least another 5 years, longer if running a Linux distro. This is assuming that at some point, that Microsoft will make a decision in regards to how 'new' a system has to be for the latest Windows 10, yet this won't stop the computers from finding another way to get online, be it Windows 7, 8.1 or Linux. So boycotting targeted machines by age won't be the answer, Intel needs to be held civilly and/or criminally responsible (if a coverup is discovered & proven for the latter). With as many Intel employees and interns that's worked for them in the last two decades, it's kind of hard for any reasonable person to believe that no one seen anything wrong all of these years.
If this were the automotive industry being discussed at this moment, Congress would already had gotten involved. There are more computers in homes and businesses than vehicles on US streets & highways combined, this is a national security issue & should be treated as such. Intel has the cash reserves to remedy this crisis, under the right duress they would. Even if there's a major short term loss (there would be), Intel would still ride this out, just as other notable corporations (Exxon, BP & Toyota) did, plus regain confidence of their customers by doing what's right for everyone, to include themselves, in making the slate clean.
Cat
TsofT - 6 years ago
Ugh, this comment system sucks... editing so I can reply to the correct comment
TsofT - 6 years ago
sudo apt-get update
sudo apt-get install iucode-tool
sudo update-initramfs -k all -u
Reboot... Done...
SuperSapien64 - 6 years ago
Wow that simple huh?
cat1092 - 6 years ago
"sudo apt-get update
sudo apt-get install iucode-tool
sudo update-initramfs -k all -u
Reboot... Done..."
You know for certain this won't cause a 'boot loop' for all computers running Linux? Some of which once didn't support it (such as late model Samsung/Lenovo notebooks), yet now does, maybe because of a UEFI update and/or Linux kernel changes.
The boot loop issue can be fixed only by the OEM', not a local shop or DIY enthusiast, the UEFI chipset would need to be reprogrammed manually. Samsung has kept a tight lid on how to perform outside their repair facility. A $350+ repair that no OEM will cover, unless that version of Linux were shipped on the computer. Otherwise will hit the garbage can, minus the HDD/SSD, many aren't worth this cost of repair once 3 years old.
I have a Samsung notebook that was notorious for the boot loop, shipped with Windows 8, MB had to be replaced when upgrading to 8.1 because the kernel broke the UEFI firmware. This, among other reasons, are why Samsung exited the Windows notebook business. Not that they really need it, are now the 'cream of the crop' SSD provider, as well as a leading RAM one for OEM's, making cash hand over fist w/out the hassles of dealing with Windows.
I'd like to apply the above Terminal code, yet would like some reassurance that the firmware isn't broken again. No longer under warranty & used MB replacement is $240 minimum last time I looked. I couldn't sell the notebook for that price, the ones willing to pay that much for a used MB are far more attached to the model than myself, or used for commercial purposes where the cost would repay for itself.
Cat
TsofT - 6 years ago
What you're talking about is when the microcode is updated in the BIOS/firmware of the motherboard (in other words the motherboard maker created a bad BIOS that was then burned on the board).
What I posted does no such thing. It loads the microcode in runtime at boot and can easily be disabled. It's not permanent. In fact simply rebooting the machine will clear the microcode.
cat1092 - 6 years ago
"What you're talking about is when the microcode is updated in the BIOS/firmware of the motherboard (in other words the motherboard maker created a bad BIOS that was then burned on the board).
TsofT, thanks for the follow up post, will ease the minds of those with vulnerable make/model computers.;-)
Cat